Whoa!
I remember the first time I fired up a Secret Network node for real testing and thought, this is different.
It wasn’t just privacy talk; the interplay between private smart contracts and cross-chain transfers via IBC felt like a whole new playground.
Initially I thought validators were all the same, but after a couple of missed blocks and one close call with a slash event, my view changed—fast.
Here’s the thing: the wallet you use, the validator you stake with, and how you manage your keys shape your whole Secret Network experience, especially when you’re doing staking and IBC transfers.
Hmm… seriously, something felt off about blindly following validator “top lists.”
My gut told me to dig deeper than APY numbers.
On one hand, high commission can be annoying, though actually low commission alone isn’t a guarantee of reliability.
And on the other hand, a validator with great uptime but poor governance participation might still be risky for long-term stakers.
So I started tracking node health, voting records, and community engagement—little things that matter.
Whoa!
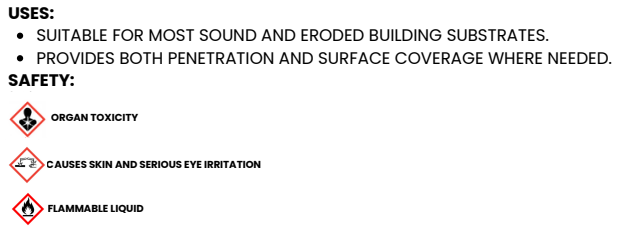
A practical checklist helped.
Check node uptime and missed block history.
Look for on-chain governance participation, social communication, and clear slashing policies from the operator.
If a validator is obscure and never interacts with proposals, consider it a yellow flag—especially if you care about decentralization and the network’s long-term security.
![]()
Wallets, IBC, and the Keplr Moment
Wow!
Okay, so check this out—wallet choice really matters when you want to do IBC transfers into Secret-powered dapps while keeping private contract interactions intact.
I’m biased, but using a browser extension that supports Cosmos chains and IBC is the easiest path for most folks.
I use the keplr wallet extension for day-to-day interactions because it balances UX and control without making me jump through too many hoops.
That said, always consider hardware wallet pairing for real security if you’re holding meaningful funds.
Whoa!
Seriously? Yeah.
There are subtle UX quirks with IBC routes and memo fields that can brick transfers if you rush.
So test with tiny amounts first—this is boring but very very important.
And remember: privacy-preserving contracts sometimes require extra permissions, so read that pop-up—don’t just click through.
Wow!
Validator selection isn’t just about who yields the most SCRT today.
It’s about resilience, reputation, and alignment with the community’s values—plus geographic diversity for censorship resistance.
I once picked a cheaply-run validator and paid a price with downtime during a maintenance mishap; the small percentage commission I saved didn’t cover the learning curve or stress.
Lesson learned—pay a reasonable commission for trustworthy ops, or at least diversify stakes across a few reliable validators.
Practical Steps for Choosing Validators on Secret Network
Whoa!
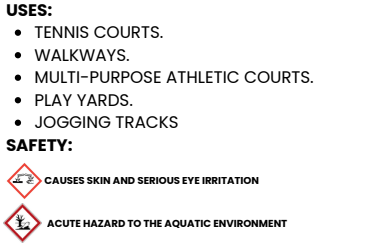
Start simple.
Verify uptime stats and check for recent slash events in the explorer.
Look up the operator’s documentation and communication channels; if they answer questions and publish runbooks, that matters a lot.
Also, consider delegating to multiple validators to spread risk, but keep network decentralization in mind so you’re not just shifting centralization around.
Hmm… my instinct said to check the validator’s infrastructure stack.
Do they run multiple nodes in different regions?
Do they use auto-updates or a tested CI pipeline?
A validator that can explain their backup and recovery plan is more credible than one that can’t—so ask for those details.
And oh, mock audits or public node metrics are a nice-to-have, not a requirement, but they show maturity.
Whoa!
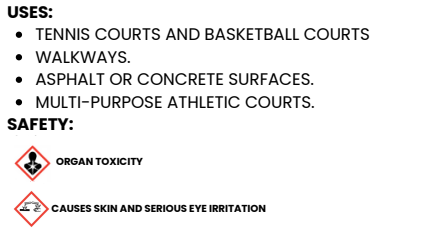
Consider governance behavior.
Validators who vote regularly and explain their rationale help keep the chain healthy.
On the flip side, validators that abstain or don’t reveal their stance can be a governance risk, especially for networks where social coordination matters.
If you care about privacy-first outcomes, align with validators that support hardening privacy features and reject proposals that weaken confidentiality guarantees.
Operational Tips: Staking, Unbonding, and Slashing
Wow!
Staking is a commitment.
Unbonding periods vary, and during that time you’re vulnerable to market moves and can’t participate in voting.
If you’re doing IBC and activity-heavy dapps, factor in liquidity needs and choose validators accordingly.
Also, keep a small operational buffer of tokens that you won’t stake so you can cover fees or emergency IBC reroutes.
Whoa!
Slashing is painful.
It happens for double-signing or extended downtime, and it cuts a portion of your stake immediately.
Fragment your stake across multiple validators to mitigate risk, but don’t dilute your governance voice so much that you can’t meaningfully vote.
Balance is the name of the game—yeah, it’s annoying to think in percentages and probabilities, but that’s crypto for you.
FAQ
How do I safely use Keplr with Secret Network?
Wow!
Pair the extension with a hardware wallet for best safety.
Test IBC transfers with tiny amounts before moving large sums.
Keep the extension updated and only approve transactions you understand.
And keep a seed phrase backup offline, not on cloud notes or screenshots.
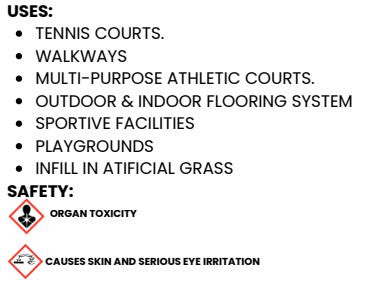
What should I look for in a validator’s profile?
Whoa!
Uptime, no recent slashes, active governance voting, public communication channels, and clear infrastructure explanations are primary.
Medium-sized operators with transparent practices often outperform unknown low-commission validators.
Also consider geographic distribution and whether the operator contributes to ecosystem tooling or education.